Authenticated encryption – data security with AES-GCM
Confidentiality and integrity in one standardized scheme
Introduction
Encrypting data is fundamental to modern IT systems. But encryption alone is not enough. Besides confidentiality, you must ensure that data cannot be altered undetected.
Modern cryptographic schemes therefore combine encryption and integrity protection in a single algorithm. These are called authenticated encryption schemes.
A widely deployed example is AES-GCM.
Confidentiality vs. integrity
Classical encryption only protects confidentiality. An attacker can still modify ciphertext, for example by:
- flipping bits
- swapping blocks
- appending data
If the system does not detect such changes, the consequences can be severe.
Authenticated encryption
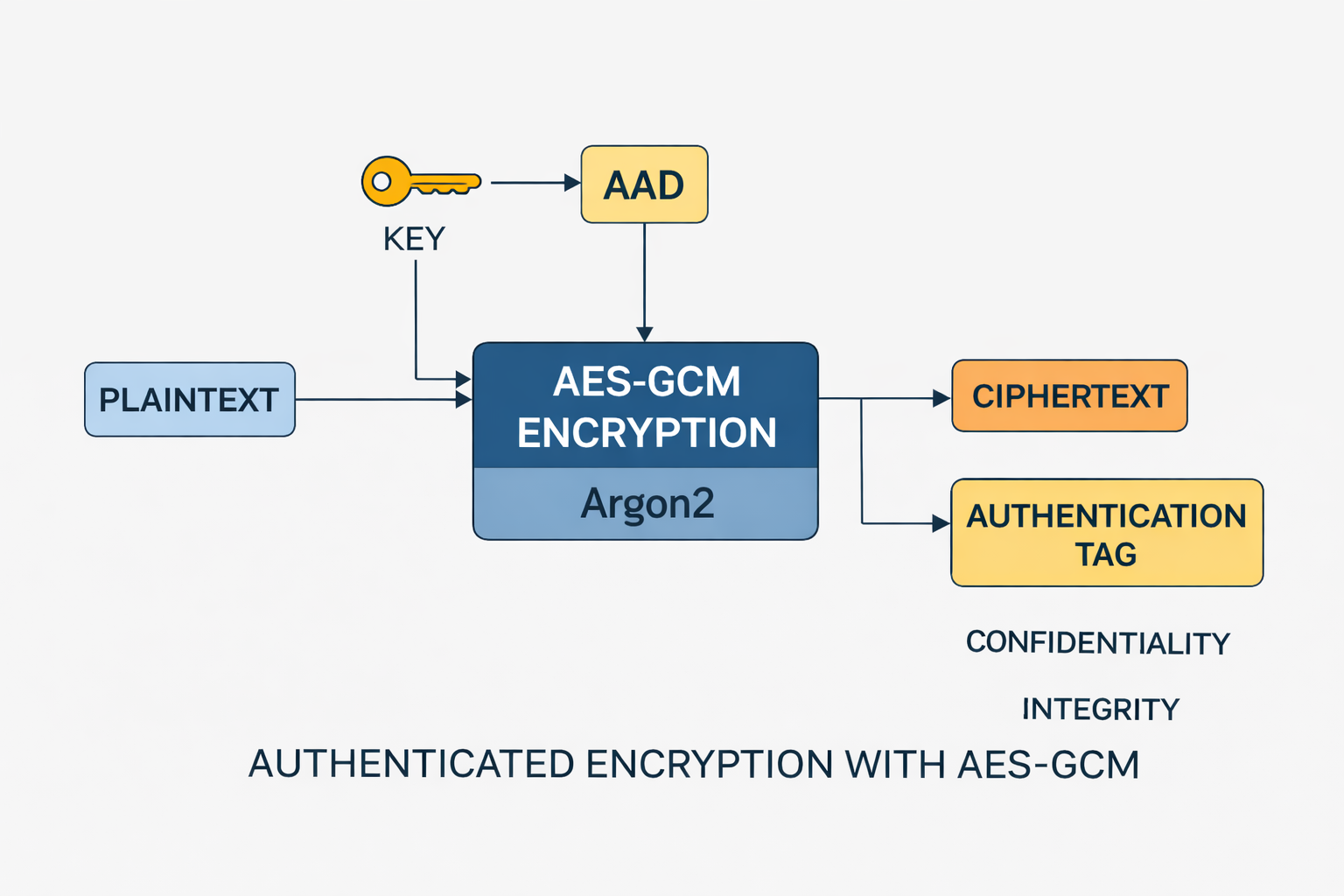
Authenticated encryption addresses this by combining two properties:
- encryption of the payload
- integrity checking
The result is an authentication tag. If the tag is wrong, decryption is rejected.
AES – the standard for symmetric encryption
AES (Advanced Encryption Standard) is today’s dominant block cipher. It was standardized by NIST and is used in many applications:
- TLS
- VPNs
- full-disk encryption
- secure storage
AES uses 128-bit blocks and several key lengths. The most common variant is AES-256.
AES security in numbers
AES security depends on key length. AES-256 is especially relevant.
An AES-256 key has:
- 2256 possible values
- roughly 1.16 × 1077 keys
For comparison: even if a very fast machine could test 1 trillion (1012) keys per second, exhaustive search would still take on the order of about 3.6 × 1057 years.
The age of the universe is about 13.8 billion years (1.38 × 1010 years) – brute-forcing AES-256 is therefore practically impossible.
Where is the risk then?
In practice AES is not broken by raw compute; failures come from implementation and usage.
Typical weaknesses:
- nonce reuse (especially critical for AES-GCM)
- weak or incorrectly generated keys
- unsafe implementations
- side-channel attacks (timing, power analysis)
- incorrect use of authenticated encryption
Especially with AES-GCM: reusing a nonce can destroy security entirely.
Role of quantum computers
People often ask whether quantum computers threaten AES. With Grover’s algorithm, effective security in bits is roughly halved: AES-256 is about as strong as AES-128 against an ideal quantum attacker.
Bottom line: AES-256 remains practically secure in the quantum era as long as the implementation is sound.
Why AES-GCM is standard today
AES alone only provides confidentiality. AES-GCM additionally provides:
- protection against tampering (authentication tag)
- protection against replay and forgery when used correctly
That is why AES-GCM appears in:
- HTTPS (TLS 1.2 / 1.3)
- VPNs
- cloud storage
- modern APIs
Galois/Counter Mode (GCM)
GCM is a mode of operation for AES and combines two ideas:
- Counter mode: turns AES into a fast stream-cipher-like construction.
- Galois-field authentication: checks integrity using arithmetic in a Galois field.
The result is a 128-bit authentication tag.
Additional authenticated data (AAD)
AES-GCM supports AAD: data that is not encrypted but is included in the integrity check.
Typical examples:
- metadata
- protocol fields
- headers
If AAD is altered, authentication fails.
Advantages of AES-GCM
- high speed
- parallelizable
- built-in integrity
- widely available implementations
That is why AES-GCM is used in many modern protocols.
Applications
Authenticated encryption appears in many systems:
- secure storage
- cloud storage
- password managers
- communication protocols
Conclusion
AES is cryptographically very strong; real attacks almost always target implementation mistakes or misuse. AES-GCM is safe when nonces and keys are handled correctly.
AES-GCM is a powerful scheme that provides confidentiality and integrity together. Combining AES encryption with mathematical authentication yields a robust security design for modern applications.
In short: AES is rarely the problem – usage decides security.
Author: Ruedi von Kryentech
Created: 6 Apr 2026 · Last updated: 6 Apr 2026
Technical content as of the last update.