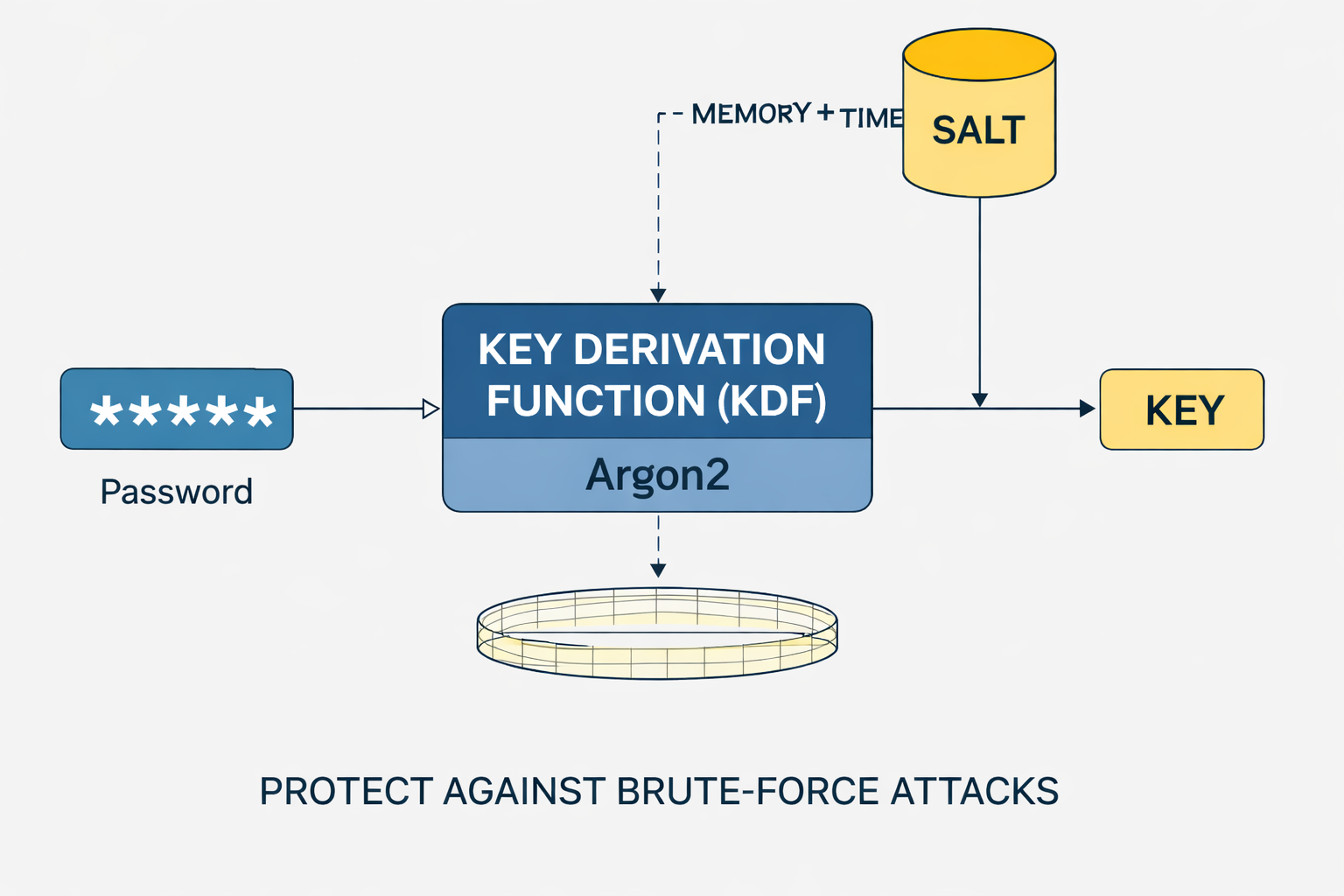
Key derivation functions – protection against brute-force attacks
Why KDFs such as Argon2 are central to modern password security
Introduction
In modern security systems it is not sufficient to use a password directly as a cryptographic key. Passwords typically have limited entropy and are therefore vulnerable to systematic attacks such as brute-force or dictionary attacks.
A key derivation function (KDF) transforms such a password into a secure key by deliberately increasing computation time and memory use. That artificially raises the cost of every single guess.
In systems such as VisuKey, this step is especially critical: a stable key is derived from a biometric or image-based input (e.g. an image embedding). Because that input is not perfectly deterministic, the KDF must also ensure that small variations do not lead to trivially guessable keys.
The combination of signal processing, error correction, and key derivation thus forms the foundation for secure, image-based authentication systems.
The problem of simple passwords
From an information-theoretic perspective, a password is a source with limited entropy. Even when the search space looks large, effective security is often much lower because users do not choose random strings.
A typical example:
62⁸ ≈ 2.18 × 10¹⁴ possible combinations
A modern attacker can, however, use GPUs or specialized hardware (ASICs) to perform billions of hash evaluations per second. That drastically reduces the effective attack time.
The fundamental issue is:
- Passwords are not uniformly distributed
- Passwords have low effective entropy
- Passwords are attackable offline once a hash is available
VisuKey faces a similar problem: An image or its embedding is not a perfect random value. The resulting bit structure contains correlations and reduced entropy that would be exploitable without additional hardening.
Basic principle of key derivation
Formally, a key derivation function can be described as a deterministic mapping:
K = KDF(P, S, C)
where:
- P: password or raw input (e.g. embedding)
- S: salt (random, non-secret value)
- C: cost parameters (time, memory, parallelism)
The salt serves two central purposes:
- It prevents identical keys when inputs are the same
- It eliminates precomputed attacks (rainbow tables)
The KDF itself is constructed so that it:
- is not efficiently invertible
- allows no structural shortcuts
- is deliberately unfriendly to specialized hardware
Even if an attacker knows the salt (which is common), the key remains protected because security rests not on secrecy of the salt but on the complexity of the KDF.
In VisuKey this step is applied after the signal is stabilized to produce a cryptographically secure key from a corrected bit pattern.
Example: from password to key
Consider a concrete example to understand how a key derivation function works.
Given:
- Password:
myPassword123 - Salt:
0xA7F3C91B(randomly generated) - Parameters: Argon2id with m = 64 MB, t = 3, p = 2
The KDF computes:
K = Argon2id("myPassword123", Salt, Parameters)
The result is an apparently random bit string, e.g.:
0x9f3a7c2d...b81e
Important properties:
- The output is deterministic (same input → same key)
- Even tiny password changes yield completely different results
- The key is not recoverable by reversing the function
The password is not “encrypted” in the usual sense; it is processed through a one-way, intentionally expensive transformation.
Time-based cost
A central property of modern KDFs is controlled increase of computation time. This is typically achieved through iterations or sequential dependencies.
The total effort of a brute-force attack can be approximated by:
T ≈ N × tKDF
where:
- N: number of possible candidates
- tKDF: time per KDF evaluation
Example:
- tKDF = 100 ms
- N = 10⁹
→ T ≈ 3 years
For legitimate users this delay is barely noticeable, but for attackers it becomes exponentially expensive.
Memory-based cost
A decisive advance in modern KDFs is the introduction of memory hardness. The algorithm is constructed so that large memory regions are required.
That leads to two effects:
- Reduced parallelization on GPUs
- Higher hardware cost for specialized attacks
While CPUs have large, flexible memory, memory per GPU thread is strongly limited.
A memory-intensive KDF therefore forces the attacker either:
- to run fewer threads in parallel
- or to deploy massively more hardware
This mechanism is exactly what makes Argon2 especially effective.
Argon2 – modern standard
Argon2 is based on a memory-intensive construction in which large memory blocks are filled iteratively and combined.
Computation proceeds in several phases:
- Initialize memory with password and salt
- Multiple passes over the memory
- Data-dependent or data-independent access patterns
The variants differ in access behavior:
- Argon2d: data-dependent → fast but vulnerable to side channels
- Argon2i: data-independent → safer against side channels
- Argon2id: hybrid variant → recommended
Argon2 parameters
Argon2’s security is fully determined by its parameters:
- Memory cost (m): size of memory used
- Time cost (t): number of iterations
- Parallelism (p): number of parallel threads
These parameters define resource consumption per hash and thus directly the cost of an attack.
In security-critical applications, typical values are:
- m = 64–256 MB
- t = 2–4
- p = 2–4
The optimal choice is highly system-dependent and should be determined empirically.
Application in VisuKey
In VisuKey a KDF is not applied directly to a password but to a feature vector derived from an image.
The typical flow is:
- Image → embedding (e.g. neural network)
- Binarization of the embedding
- Error correction (e.g. BCH code)
- KDF (Argon2) → final key
The KDF serves several roles at once:
- Increases entropy of the resulting key
- Prevents structural attacks on the embedding
- Hardens against brute-force reconstruction of similar images
Especially important is the combination with error correction, because small variations in the input signal must be stabilized before the KDF.
Conclusion
Key derivation functions are a central part of modern cryptographic systems. They transform low-entropy inputs into robust keys and deliberately raise the cost for attackers.
With Argon2, a method is available today that combines both time- and memory-based hardening and is tuned against modern hardware attacks.
In systems such as VisuKey, the KDF is a critical link between signal processing and cryptography and enables secure key derivation from imperfect real-world data.
Author: Ruedi von Kryentech
Created: 6 Apr 2026 · Last updated: 6 Apr 2026
Technical content as of the last update.